Nixpacks
Coming from the README.md
2 months ago, I discovered Nixpacks - an alternative to Buildpacks to build a final container image that simply works. I’ve tried it with multiple projects, and the promise is very good. I feel it is less black magic than Buildpacks and easily extensible. In this article, I will share my feedback on the pros and the cons of this emerging project. Let's go!
Nixpacks is available on Linux, MacOS, and Windows. You must also have Docker installed and running since Nixpacks relies on it. Once it's installed, you can execute the "nixpacks" cli command:
nixpacks 0.3.1
USAGE:
nixpacks [OPTIONS]
OPTIONS:
--apt ... Provide additional apt packages to install in the environment
-b, --build-cmd Specify the build command to use
--env ... Provide environment variables to your build
-h, --help Print help information
-i, --install-cmd Specify the install command to use
--libs ... Provide additional nix libraries to install in the
environment
-p, --pkgs ... Provide additional nix packages to install in the environment
--pin Pin the nixpkgs
-s, --start-cmd Specify the start command to use
-V, --version Print version information
SUBCOMMANDS:
build Create a docker image for an app
help Print this message or the help of the given subcommand(s)
plan Generate a build plan for an app
Here are the pros and the cons coming from what I've tried and seen:
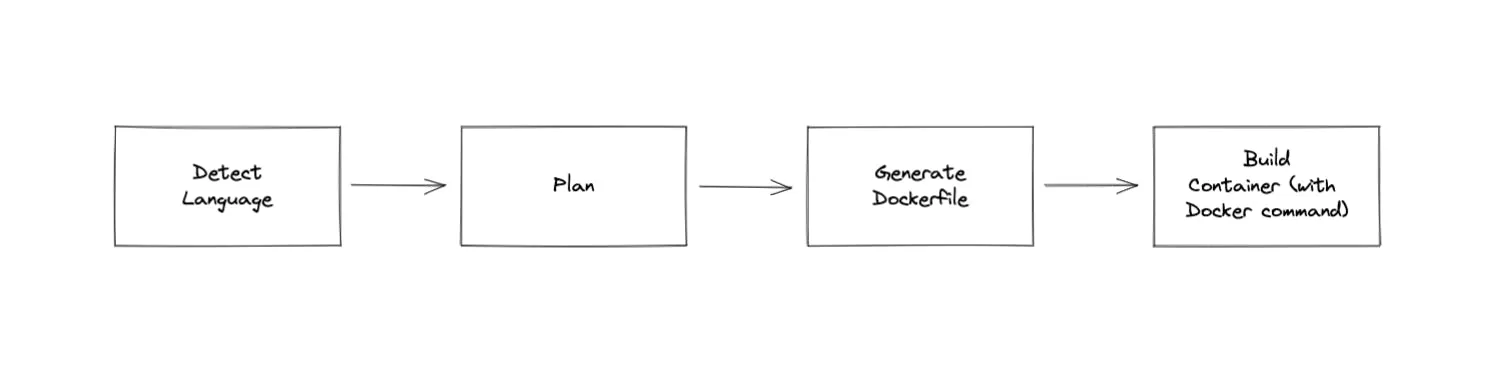
It’s similar to Buildpacks but better since it generates a Dockerfile file and builds it with a NIX binary. Here is a schema of the process done by Nixpacks.
A plan looks like this:
~/I/q/console (staging|✔) $ nixpacks plan .
{
"version": "0.0.24",
"setup": {
"pkgs": [
{
"name": "nodejs"
},
{
"name": "yarn"
}
],
"libraries": [],
"apt_pkgs": [],
"baseImage": "ghcr.io/railwayapp/nixpacks:debian-1655126806"
},
"install": {
"cmd": "yarn install --frozen-lockfile --production=false"
},
"build": {
"cmd": "yarn run build"
},
"start": {
"cmd": "yarn run start"
},
"variables": {
"NODE_ENV": "production",
"NPM_CONFIG_PRODUCTION": "false"
},
"static_assets": {}
}
Understandable Errors
The usage of NIX makes errors understandable when something goes wrong, which is a convenient advantage compared to Buildpacks. For instance, when running "nixpacks build ." for one of my Strapi applications, I got the following error:
~/I/o/strapi-v4 (main|✔) $ nixpacks build .
\=== Building (nixpacks v0.0.24) ===
\=> Packages
-> nodejs-12_x
-> yarn { nodejs = nodejs-12_x }
\=> Install
-> yarn install --frozen-lockfile --production=false
\=> Build
-> yarn run build
\=> Start
-> yarn run start
[+] Building 1.3s (8/12)
=> [internal] load build definition from Dockerfile 0.0s
=> => transferring dockerfile: 464B 0.0s
=> [internal] load .dockerignore 0.0s
=> => transferring context: 87B 0.0s
=> [internal] load metadata for ghcr.io/railwayapp/nixpacks:debian-1655126806 0.5s
=> [1/8] FROM ghcr.io/railwayapp/nixpacks:debian-1655126806@sha256:3d33b3f942fff25f99270e78177fe5ea39ce94b4090c5af336131a4a3d12794d 0.0s
=> [internal] load build context 0.1s
=> => transferring context: 477.36kB 0.0s
=> CACHED [2/8] WORKDIR /app/ 0.0s
=> CACHED [3/8] COPY environment.nix /app/ 0.0s
=> ERROR [4/8] RUN nix-env -if environment.nix 0.7s
\------
> [4/8] RUN nix-env -if environment.nix:
#8 0.359 installing 'env'
#8 0.649 error: Package ‘nodejs-12.22.12’ in /nix/store/j86dwr6jqjrk1m7z7b1sk3wh8zswjpa7-nixpkgs/nixpkgs/pkgs/development/web/nodejs/v12.nix:11 is marked as insecure, refusing to evaluate.
#8 0.649
#8 0.649
#8 0.649 Known issues:
#8 0.649 - This NodeJS release has reached its end of life. See https://nodejs.org/en/about/releases/.
#8 0.649
#8 0.649 You can install it anyway by allowing this package, using the
#8 0.649 following methods:
#8 0.649
#8 0.649 a) To temporarily allow all insecure packages, you can use an environment
#8 0.649 variable for a single invocation of the nix tools:
#8 0.649
#8 0.649 $ export NIXPKGS_ALLOW_INSECURE=1
#8 0.649
#8 0.649 Note: For `nix shell`, `nix build`, `nix develop` or any other Nix 2.4+
#8 0.649 (Flake) command, `--impure` must be passed in order to read this
#8 0.649 environment variable.
#8 0.649
#8 0.649 b) for `nixos-rebuild` you can add ‘nodejs-12.22.12’ to
#8 0.649 `nixpkgs.config.permittedInsecurePackages` in the configuration.nix,
#8 0.649 like so:
#8 0.649
#8 0.649 {
#8 0.649 nixpkgs.config.permittedInsecurePackages = [
#8 0.649 "nodejs-12.22.12"
#8 0.649 ];
#8 0.649 }
#8 0.649
#8 0.649 c) For `nix-env`, `nix-build`, `nix-shell` or any other Nix command you can add
#8 0.649 ‘nodejs-12.22.12’ to `permittedInsecurePackages` in
#8 0.649 ~/.config/nixpkgs/config.nix, like so:
#8 0.649
#8 0.649 {
#8 0.649 permittedInsecurePackages = [
#8 0.649 "nodejs-12.22.12"
#8 0.649 ];
#8 0.649 }
#8 0.649 (use '--show-trace' to show detailed location information)
\------
executor failed running [/bin/bash -ol pipefail -c nix-env -if environment.nix]: exit code: 1
Error: Docker build failed
In my experience, this error message is much more understandable than Buildpacks but still hard to interpret for a neophyte in building apps with Docker and NIX.
Applications written in PHP are hard to containerize. I spent (wasted) hours with Qovery users deploying their Laravel apps because they need a web server (NGINX/Apache) and to run 3 to 4 processes inside a container. Just to give you the perspective of the complexity, here is a Dockerfile I’ve written for a hello world PHP Laravel app 😕
FROM php:8.1-fpm
# Set working directory
WORKDIR /var/www
# Add docker php ext repo
ADD https://github.com/mlocati/docker-php-extension-installer/releases/latest/download/install-php-extensions /usr/local/bin/
# Install php extensions
RUN chmod +x /usr/local/bin/install-php-extensions && sync && \\
install-php-extensions mbstring pdo_mysql zip exif pcntl gd memcached
# Install dependencies
RUN apt-get update && apt-get install -y \\
build-essential \\
libpng-dev \\
libjpeg62-turbo-dev \\
libfreetype6-dev \\
locales \\
zip \\
jpegoptim optipng pngquant gifsicle \\
unzip \\
git \\
curl \\
lua-zlib-dev \\
libmemcached-dev \\
nginx
# Install supervisor
RUN apt-get install -y supervisor
# Install composer
RUN curl -sS https://getcomposer.org/installer | php -- --install-dir=/usr/local/bin --filename=composer
# Clear cache
RUN apt-get clean && rm -rf /var/lib/apt/lists/*
# Add user for laravel application
RUN groupadd -g 1000 www
RUN useradd -u 1000 -ms /bin/bash -g www www
# Copy code to /var/www
COPY --chown=www:www-data . /var/www
# add root to www group
RUN chmod -R ug+w /var/www/storage
# Copy nginx/php/supervisor configs
RUN cp docker/supervisor.conf /etc/supervisord.conf
RUN cp docker/php.ini /usr/local/etc/php/conf.d/app.ini
RUN cp docker/nginx.conf /etc/nginx/sites-enabled/default
# PHP Error Log Files
RUN mkdir /var/log/php
RUN touch /var/log/php/errors.log && chmod 777 /var/log/php/errors.log
# Deployment steps
RUN composer install --optimize-autoloader --no-dev
RUN chmod +x /var/www/docker/run.sh
EXPOSE 80
ENTRYPOINT ["/var/www/docker/run.sh"]
And with Nixpacks, you just need to run "nixpacks build .":
~/I/o/test-laravel $ nixpacks build .
\=== Building (nixpacks v0.0.24) ===
\=> Packages
-> php80
-> perl
-> nginx
-> php80Packages.composer
-> nodejs
\=> Install
-> mkdir -p /var/log/nginx && mkdir -p /var/cache/nginx && composer install && npm i
\=> Build
-> npm run prod
\=> Start
-> ([ -e /app/storage ] && chmod -R ugo+w /app/storage); perl /assets/transform-config.pl /assets/nginx.template.conf /nginx.conf && echo "Server starting on port $PORT" && (php-fpm -y /assets/php-fpm.conf & nginx -c /nginx.conf)
[+] Building 29.6s (16/16) FINISHED
=> [internal] load build definition from Dockerfile 0.1s
=> => transferring dockerfile: 826B 0.0s
=> [internal] load .dockerignore 0.0s
=> => transferring context: 2B 0.0s
=> [internal] load metadata for ghcr.io/railwayapp/nixpacks:debian-1655126806 0.4s
=> [internal] load build context 1.1s
=> => transferring context: 19.06MB 1.1s
=> [ 1/11] FROM ghcr.io/railwayapp/nixpacks:debian-1655126806@sha256:3d33b3f942fff25f99270e78177fe5ea39ce94b4090c5af336131a4a3d12794d 0.0s
=> CACHED [ 2/11] WORKDIR /app/ 0.0s
=> CACHED [ 3/11] COPY environment.nix /app/ 0.0s
=> CACHED [ 4/11] RUN nix-env -if environment.nix 0.0s
=> [ 5/11] COPY assets/transform-config.pl /assets/transform-config.pl 0.1s
=> [ 6/11] COPY assets/php-fpm.conf /assets/php-fpm.conf 0.0s
=> [ 7/11] COPY assets/nginx.template.conf /assets/nginx.template.conf 0.0s
=> [ 8/11] COPY . /app/ 0.6s
=> [ 9/11] RUN mkdir -p /var/log/nginx && mkdir -p /var/cache/nginx && composer install && npm i 22.0s
=> [10/11] RUN npm run prod 3.3s
=> [11/11] COPY . /app/ 0.5s
=> exporting to image 1.4s
=> => exporting layers 1.4s
=> => writing image sha256:73e260fcd8fd69a76db8e81ae816b62237b613877cd0e87f7ed41eed1a13ad12 0.0s
=> => naming to docker.io/library/f4cc686f-5c91-4e41-ad98-999fda42fa0f 0.0s
Use 'docker scan' to run Snyk tests against images to find vulnerabilities and learn how to fix them
\=== Successfully Built! ===
Run:
docker run -it f4cc686f-5c91-4e41-ad98-999fda42fa0f
This example convinced me to go further in trying Nixpacks.
I've noticed that Docker is not well known by most frontend developers; Nixpacks would be super useful here to make frontend app deployment on Kubernetes easier. Unfortunately, I didn't manage to build our Qovery v3 console React app with Nixpacks. It's a real app with different kinds of dependencies, and this is where it fails. Python seems to be required for a library. I think it is fixable with not too much effort, but it does not work out of the box.
In this case, with a brand new simple "hello world" react app it works
~/I/o/react-app (main|✔) $ nixpacks build .
\=== Building (nixpacks v0.0.24) ===
\=> Packages
-> nodejs
\=> Install
-> npm ci
\=> Build
-> npm run build
\=> Start
-> npm run start
[+] Building 59.8s (13/13) FINISHED
=> [internal] load build definition from Dockerfile 0.0s
=> => transferring dockerfile: 419B 0.0s
=> [internal] load .dockerignore 0.0s
=> => transferring context: 2B 0.0s
=> [internal] load metadata for ghcr.io/railwayapp/nixpacks:debian-1655126806 0.3s
=> [1/8] FROM ghcr.io/railwayapp/nixpacks:debian-1655126806@sha256:3d33b3f942fff25f99270e78177fe5ea39ce94b4090c5af336131a4a3d12794d 0.0s
=> [internal] load build context 10.0s
=> => transferring context: 223.77MB 9.9s
=> CACHED [2/8] WORKDIR /app/ 0.0s
=> [3/8] COPY environment.nix /app/ 0.5s
=> [4/8] RUN nix-env -if environment.nix 10.9s
=> [5/8] COPY . /app/ 2.7s
=> [6/8] RUN npm ci 23.0s
=> [7/8] RUN npm run build 5.6s
=> [8/8] COPY . /app/ 3.6s
=> exporting to image 3.1s
=> => exporting layers 3.1s
=> => writing image sha256:6eec677e41fb2c2a218207e97fefd4ddbeb9bae5448367cc5726160310cd7f1b 0.0s
=> => naming to docker.io/library/c9330f44-3258-46a7-a489-ea2af6107834 0.0s
Use 'docker scan' to run Snyk tests against images to find vulnerabilities and learn how to fix them
\=== Successfully Built! ===
Run:
docker run -it c9330f44-3258-46a7-a489-ea2af6107834
Nixpacks is a promising alternative to Buildpacks, and I am pretty sure it will be well received by the open-source community. We even consider using it in Qovery as soon as we are confident in its future. The team behind made a very good job in providing an elegant solution to a complex problem - building a final OCI image without necessarily spending time to write a Dockerfile while keeping it auditable via a "nixpacks plan" command.

Romaric founded Qovery to make Kubernetes accessible to every engineering team. He writes about platform strategy, developer experience, and the future of cloud infrastructure.
Qovery ensures every agent action is scoped, audited, and policy-checked. Start deploying in under 10 minutes.