Check out our updated documentation to learn more about how Qovery works.
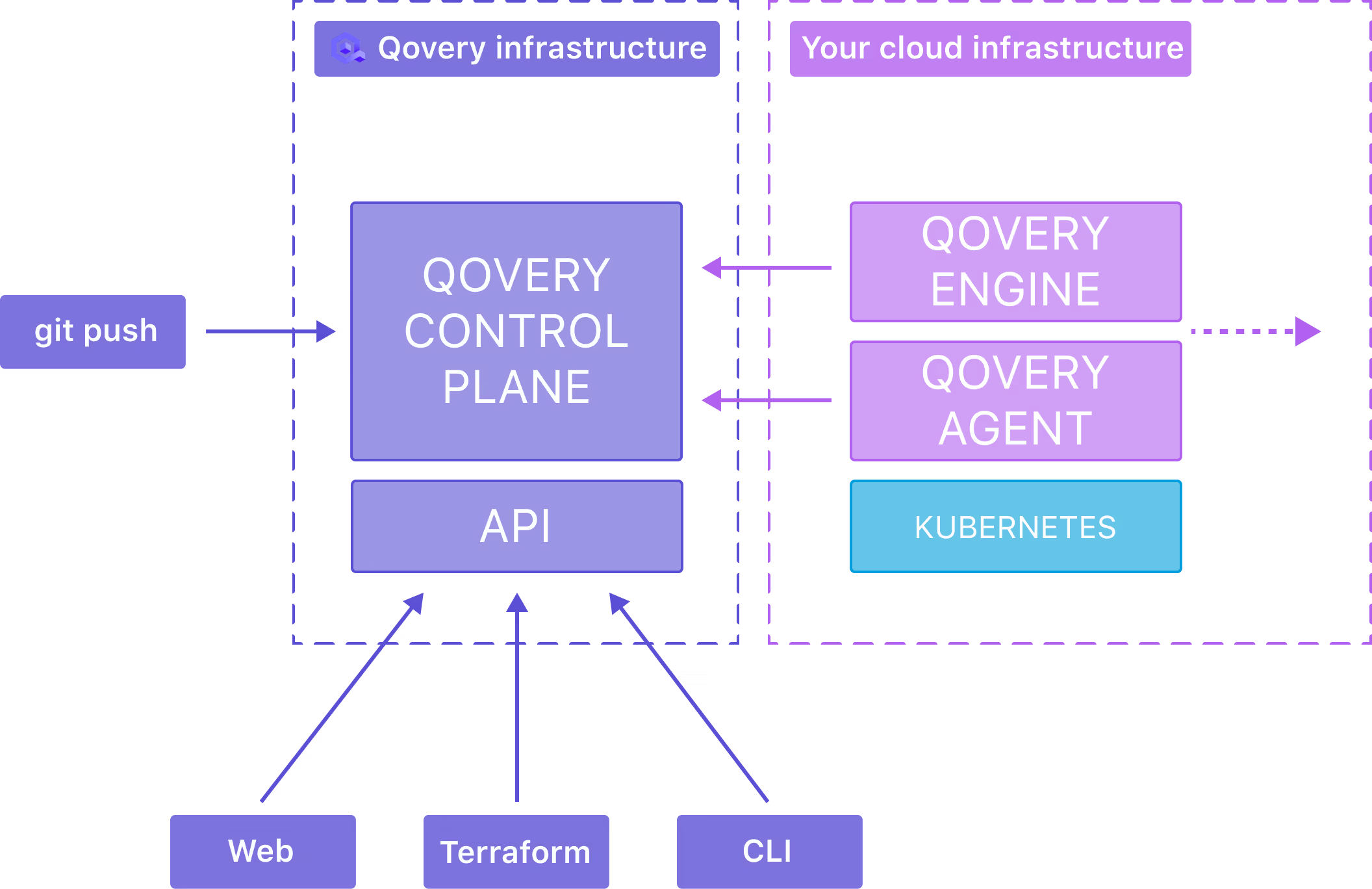
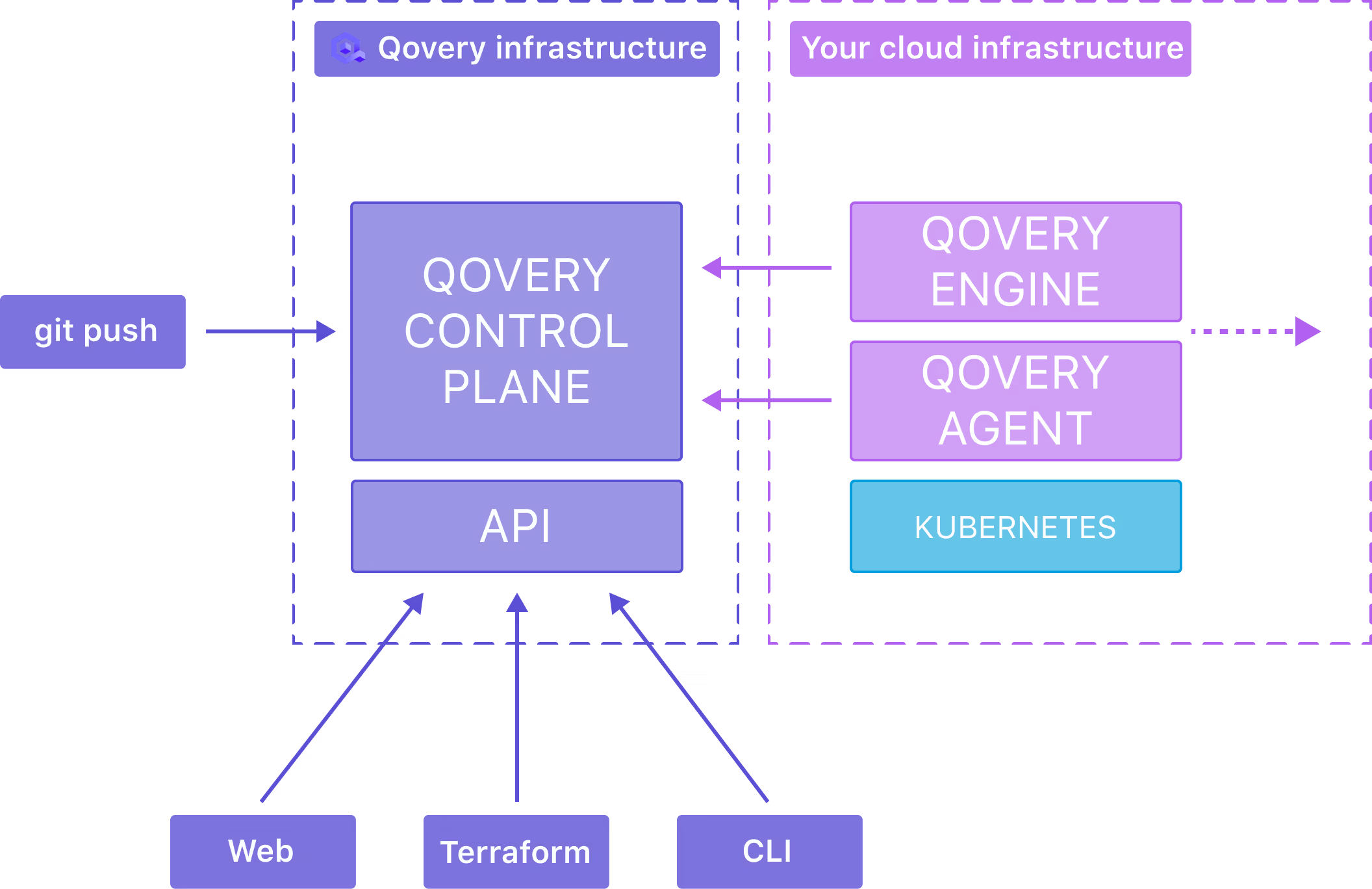
Transparency is essential when running production infrastructure. As we are onboarding more and more customers, we strive to make Qovery as open as possible and fully transparent on how it manages your applications.

Check out our updated documentation to learn more about how Qovery works.
You will learn:

Romaric founded Qovery to make Kubernetes accessible to every engineering team. He writes about platform strategy, developer experience, and the future of cloud infrastructure.
Qovery ensures every agent action is scoped, audited, and policy-checked. Start deploying in under 10 minutes.